Owner-operator Norman Camamile found himself on the weekend of June 8-9 moored with his reefer trailer at a Columbus, Ohio, area truck stop, when he saw an enticing prospect for a local load posted to DAT by someone who purported to be with Prestigious Logistics, a Memphis-based broker in business since 2020. "It was what looked like a 100-mile run or so," power only and paying quite well, he said. So much so that he could easily just drop his reefer where it was, do the work, and deadhead back with plenty of profit.
So he did, communicating all the while with an individual on the other end of a gmail address using the "Iluminati" surname. This wasn't the only load he'd seen posted with this email or another, different variant with the same Iluminati surname. If it sounds familiar to you, Overdrive reader, you'll know the about the 'Iluminati' series of phishing hacks of brokers' DAT accounts that resulted in hundreds of what appeared to be Amazon loads posted to the DAT boards, as reported last week by Alex Lockie at this link.
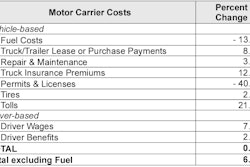
In retrospect, it all should have triggered spidey senses for owner-operator Camamile, he said, fishy as anyone calling themselves Iluminati might be, yet this all occurred a full week and more before Lockie's reporting. And Camamile was admittedly enticed by the chance to bank a little extra over a slow weekend for reefer freight. (As he noted in tandem with spot rates reporting late last week, rates have been in "abysmal territory" for him of late.)
 Norman Camamile
Norman Camamile
"I did that one," he said, and his Iluminati contact noted, "I’ve got more."
Sure thing, Camamile said. "The second run started also out of the original warehouse in Columbus but it went to a different Amazon warehouse, about 20 miles away" and paying $1,000.
Do the math. Negotiated away from the public boards directly with the Iluminati contact, Camamile was agreeing to a rate far and away above the $20/mile loads ST Freight saw posted after its DAT account was hacked last week.
[Related: 'Iluminati' hack hits DAT boards with thousands of $20/mile loads]
Camamile, running under his Cherry Tree Park Transportation authority, then went ahead and booked yet another run with the same email contact, still purporting to be with Prestigious Logistics.
By then, said Prestigious COO Tyler Ward, the company was well on its way to shutting down the hacker's ability to post loads to DAT under its account. Ward noted he woke the Saturday morning of June 8 at about 7 a.m. to his "phone blowing up. Me and my team started answering the calls," most of them owner-operator attempts to verify the details of load posts they were seeing on DAT.
Notably, owner-operator Camamile hadn't done this.
"This person had clearly gotten into our DAT account," said Ward. "I probably told 100 carriers, 'It’s not us,' the whole thing."
Company reps immediately reached out to factoring companies, as well as DAT, Ward noted, then filed reports with the FBI and the Federal Trade Commission. They communicated with Amazon, too, to "let them know the facilities we at least knew of" that seemed involved in the loads, not that they had particularly great contacts with the retail behemoth.
[Related: The 'Amazon effect,' take two: Is long-haul trucking fading away?]
"We don’t work with Amazon at all" as a freight broker, Ward said, rather focusing on a core set of shipper customers with mostly van freight, and a core group of partner carriers. Ward felt confident Prestigious had contained at least the active initial damage done by the hacker, knocking them out of the Prestigious DAT account. Amazon reps queried about this story pointed to a public blog post that outlines a reality that anyone who sees an Amazon load on a public load board like DAT should heed. Namely, the generally double brokering-focused blog post notes that the company only works with a select few third-party brokers, and furthermore, emphasis Amazon's:
Amazon does not tender loads through any third-party load boards. Any Amazon loads posted on third-party load boards will only be tendered directly to approved and onboarded carriers via the Relay web portal or Relay mobile app.
For Camamile that weekend of June 8-9, the next load was going to cost him a fair amount more than the two initial empty-Amazon-trailer moves around the Columbus area. This was a loaded trailer full of Amazon carts for its warehouse operations originating at a repair center for those carts. The owner-operator took the load from the Columbus area all the way to Mt. Juliet, Tennessee, near Nashville, then booked two more short runs of empty trailers within the Middle Tennessee region, all to and from Amazon facilities.
He would end up running four total loads, all the work taking place over that weekend of June 8-9, "when my factoring company is closed and it’s hard to get hold of people," he said. That company, crucially, is usually his go-to for credit checks and the like. "On Monday, I quickly submitted all the work I’d done to my factoring company. They called the brokerage company [Prestigious] ... a real company, a good company, but [Iluminati, of course] never worked there. The broker never heard of them. They said their system had gotten hacked as well, over the weekend."
[Related: Growing broker/carrier identity theft schemes reaping millions]
The final load picked up that same day, and Camamile was by now aware of what was going on and had no intention to follow through on the move. Yet he showed up at the pickup location nonetheless, then "asked the gate person that greeted me at the Amazon facility, 'Who’s really assigned to this work?'" as Camamile told the story. "He took a look at his list -- it was a different trucking company than my own."
In total, he was given the names of three different carriers over four loads, and said Amazon Relay reps eventually told him all of those trucking companies had been victims of phishing hacks as well. Before Camamile explicitly asked, no one at any of the facilities had bothered to question just why he was picking up the load when it was assigned to a different carrier. That kind of on-site verification is recommended in this day and age, and was a big part of a "Supply Chain Protocol" to stamp out fraud and cargo theft Overdrive has reported on in-depth in recent years.
[Related: Fight double-brokering fraud: Attorney Hank Seaton on prevention, elevating enforcement]
Overdrive subsequently spoke to one of the carriers ID'd by Amazon as assigned to at least one of Camamile's loads -- two-truck CDM Jewels, operating out of Winnsboro, South Carolina, with two owner-operators leased under their authority and in business since 2011. Being assigned an Amazon load was certainly news to CDM's Devetta Myles, who also handles IFTA, IRP and other compliance and tax matters for other independents. None of the truckers she works with are based anywhere near or commonly running on the lane between Columbus, Ohio, and Nashville, Tennessee, she noted, where Camamile's Amazon short hauls took him.
Furthermore, as far as she knew she wasn't yet fully set up in Amazon's Relay system for spot loads, though not for lack of trying.
"I tried to apply for an Amazon Relay account and they denied it" earlier this year, said Myles. Yet May 20, she received an invite to apply. "I checked the email and everything looked legit down to the verification system -- they even had two-step verifications."
Yet, speaking June 25, she had heard nothing else back since that second attempt to establish a Relay account.
A review of the email sent to Myles shows it purported to come from the carrier-ats.com domain -- the domain was created the day prior to the email being sent, May 19 of this year, registry lookup services show. The text of the email had elements similar to phishing emails sent to FMCSA-registered carriers posing as auditors, clearly phishing attempts, reported earlier this year and subsequently a couple of weeks ago as that particular scam continued.
The intro text of the May 20 email to Myles, which also cribbed from Amazon and Relay branding images:
We're thrilled to invite you to join the Amazon Relay team as an esteemed member of our trucking operations network. At Amazon Relay, we know the importance of reliable transportation in today's world. Your reputation as a dedicated carrier partner perfectly matches our commitment to setting new standards in transportation and logistics. We can't wait to have you join us as we continue to innovate the industry and provide exceptional service to our customers. Please proceed to complete the onboarding process by visiting http://carrier-ats.com or simply click the button below.
The "button" in this case was an all-caps "GET STARTED" text link (quite similar to recent FMCSA audit phishing emails that have been coming through to many registered carriers) that didn't go directly to carrier-ats.com but rather a different site.
Furthermore, the email wasn't sent just to Myles and CDM Jewels but dozens of other contact emails, presumably for carriers, at least one with a name Overdrive recognized from past contacts and coverage.
[Related: 'Fake safey audit' phishing emails keep pouring in]
"This is very broad reaching," Camamile said of what appears to be phishing hacks of both carrier and broker accounts of commonly used load platforms.
Presented with details in this story, Amazon spokesperson Sam Stephenson didn't directly confirm or deny the details, nor answer questions about the extent of scammers' infiltration of Relay's onboarding process. Rather, he noted "our teams are committed to protecting drivers from bad actors, and we actively work to combat phishing attempts made by Relay impersonators." Stephenson also pointed to the company's "work to educate our customers on how to identify fake email schemes so they are better able to protect themselves through public information sharing like blogs, email warnings, and FAQs on our website.”
Amazon reps also pointed to this public blog post with tips for recognizing phishing attempts by would-be crooks in emails. The post offers the [email protected] email address for user sanity checks, verification of suspicious emails of the type Devetta Myles received.
Owner-operator Camamile said he almost hoped Amazon would go ahead and pay at least one of the other carriers for his work in order to establish a money trail for these loads. Odds are it leads overseas outside the jurisdiction of U.S. law enforcement, but at least "there’s the money trail the FBI could follow up on," he said, maybe leading also to further lessons for carriers to avoid being hoodwinked by such schemes in the future. "Bare minimum, they might learn how the scam worked and figure out ways to stop it."
As for Camamile, he's out $400-$500 in fuel, and two days' worth of legitimate work opportunity, equivalent to $2,000 or so in revenue, he offered after a back-of-the-envelope accounting. Amazon reps queried for this story declined to answer the question of whether owner-operators like Camamile might take a particular avenue to claim at least some payment for real work performed. Ultimately, responsibility for payment lies with the shipper of any load, in this case Amazon.
For now, safe to say that if you get an unexpected email from an unknown source that ends with an invitation to all-caps GET STARTED, hyperlinked to places unknown, give it plenty scrutiny before you start down the path toward, effectively, offering up the theft of your business's identity.